Why High-Risk Industries Need Screen-Level Data Protection
In high-risk industries like energy, healthcare, finance, or manufacturing, risk is not just a concept. It is a daily reality. These sectors operate in complex environments where safety, compliance, and data sensitivity intersect. From employee health records and proprietary research to operational dashboards and regulatory documentation, the volume of sensitive data handled daily is enormous.
Industries Most at Risk, and Most Targeted
Some industries carry inherently higher stakes when it comes to information security. From operational continuity and intellectual property to patient records and national infrastructure, the sensitive data handled by these sectors makes them prime targets for both cybercriminals and insider threats.
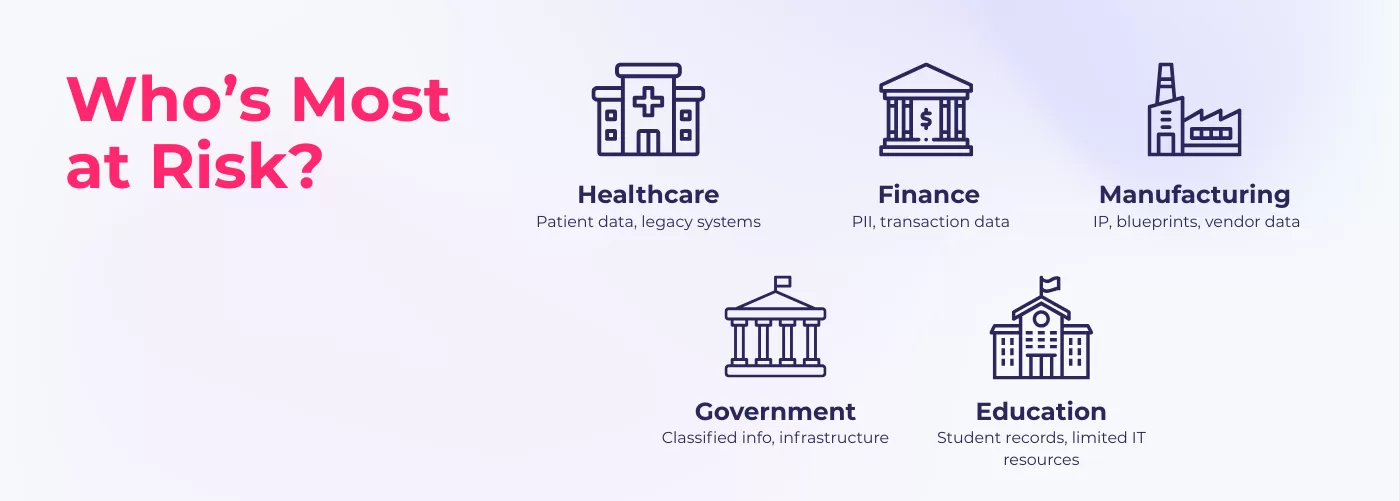
Among the most frequently targeted:
- Healthcare
From hospitals to clinics to insurance providers, healthcare organizations manage enormous volumes of sensitive data, including patient records, lab results, and billing information. This sector has consistently faced the highest average cost per breach, according to IBM. The cost of a data breach in the healthcare sector averages $9.8 million, more than double the average cost across other industries. It remains vulnerable due to legacy systems and growing digital dependencies like telehealth and cloud-based EHRs.
- Finance
Banks, fintechs, and insurance companies are natural targets due to the high volume of transactions and the sensitivity of data involved. Even one unauthorized screenshot of an internal report or trading dashboard can lead to financial loss, regulatory penalties, and irreparable trust damage. In fact, financial services companies spend an average of $6.08M dealing with data breaches, 22% higher than the global average.
- Manufacturing
Manufacturers increasingly rely on connected systems, smart devices, and data-heavy operations. But as supply chains digitize, so do their vulnerabilities. Breaches in this sector often expose blueprints, operational schedules, or supplier contracts, which can result in competitive sabotage or production delays.
- Government
From local authorities to national defense agencies, government institutions handle strategic and classified information. Breaches can compromise critical infrastructure, citizen data, or national security agendas, and the risk of insider misuse or unauthorized screen capture is particularly high in hybrid work environments.
- Education
Educational institutions store large amounts of PII for students and staff, research data, and financial records. Often operating with limited IT resources, they remain prime targets for ransomware and insider attacks, particularly as remote learning and cloud-based systems become standard.
Compliance Pressure Is Rising

Beyond the reputational and operational fallout of a data leak, industries also face increasing regulatory pressure. Compliance mandates like HIPAA, GDPR, PCI DSS, ISO 27001, and NCA ECC (in Saudi Arabia) require organizations to implement appropriate safeguards against unauthorized access and data loss, including controls that prevent internal misuse or negligence.
The challenge? Most regulations focus on access controls, encryption, and storage security. But the reality is that data can still be exposed even when those requirements are met, simply by being visible on screen. A screen left unattended, shared in a call, or captured via a phone camera could easily lead to non-compliance.
In audits and investigations, the inability to prove who accessed what data and when can be costly for organizations. That’s where screen-level protection fills a critical compliance gap.
Protect. Prove. Comply.
While most organizations have invested in securing networks, servers, and devices, one exposure point often remains unaddressed: Data displayed on screens. Whether during routine operations, remote work, or third-party collaboration, screen-level visibility can become a significant liability if not properly managed. In environments where the consequences of a leak can be financial, legal, or even life-threatening, protecting the display layer must be part of modern risk management.
What Is Screen-Level Data Protection?
Screen-level data protection refers to security measures that monitor and secure the display layer, what is shown on a user’s screen, to prevent unauthorized viewing, screen capture, or photography.
The most common and effective method? Screen Watermarking.
This involves overlaying dynamic, identifiable information (such as usernames, IP addresses, or timestamps) on top of the screen content. These watermarks:
- Deter malicious screenshots or recordings
- Increase accountability and user awareness
- Support traceability in case of data leaks
- Operate continuously without disrupting the user experience
Unlike restrictive controls that can limit workflows, screen watermarking works silently in the background, reinforcing secure behavior without impacting productivity, the best balance in fast-paced, high-stakes industries.
Real-World Use Cases
Screen watermarking is already being adopted across industries as part of broader insider threat management and zero-trust strategies.
- A healthcare organization used watermarking on internal platforms handling patient reports and lab results, ensuring any screen content, whether in-person or during a virtual consultation, carried visible identifiers, reinforcing data privacy compliance.
- A financial services firm enabled watermarking on dashboards showing real-time trading data. This discouraged screenshots during remote access, preventing sensitive information from being leaked or misused.
- A global manufacturer added screen watermarking to protect CAD designs and supplier data accessed by engineers and vendors. It prevented screenshots, boosted accountability, and supported IP compliance without disrupting workflows.
- A government agency deployed screen watermarking across sensitive systems accessed by staff and contractors. This ensured that any displayed content carried visible user identifiers, discouraging unauthorized viewing or sharing and strengthening accountability in environments vulnerable to insider risk.
The Human Element Can’t Be Ignored
Modern cybersecurity frameworks are evolving from perimeter-based to behavior-based models, and this shift is backed by real insights. According to multiple global reports, insider threats, whether malicious or accidental, now account for over 60% of data breaches. And the cost? It’s only rising year over year, reaching $17.1 million annually.
Most tools focus on detection after something has gone wrong. Screen-level protection is different. It is preventive and visual, working in real time to remind users of their responsibilities and make every session more accountable and every action responsible.
It’s not just about control. It’s about culture. Watermarking builds everyday awareness, and awareness builds trust.
In high-risk industries, data security is no longer just about firewalls, passwords, or encrypted drives. It’s about securing the entire digital environment, including what’s visible on screens. As organizations face mounting compliance demands, growing insider risks, and increasingly complex workflows, screen-level data protection emerges as a simple but powerful addition to their security stack.
For sectors where one exposed screen could mean millions in damages, the question is not whether to protect the display layer. The question is: can you afford not to?